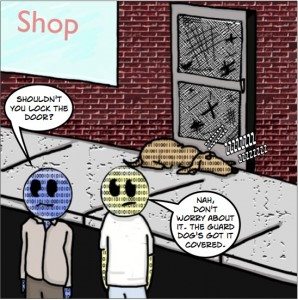
The last thing you would ever do when you leave your place of business at the end of the day is leave the door wide open.
As we have discussed in this series of posts, SSL/TLS certificates exist to not only secure web data, but they also serve as a means of identification on the Internet. When it comes time to purchase your SSL/TLS certificate, you will be presented with a number of different choices with seemingly very little differences between them. But just like anything, being able to discern the differences between Certification Authorities (CAs) means taking the time to do some research.
To save you the time of having to piece this mystery together, here are the things you need to think about when choosing a CA:
Industry Standards
Does the Certification Authority meet or exceed industry standards established by the WebTrustTM Program for Certification Authorities or the European Telecommunications Standards Institute?
Programs such as the WebTrustTM Program for Certification Authorities determine the quality of a CA from an industry perspective, assessing the CAs ability to meet high standards of confidentiality, authentication, integrity and nonrepudiation. CAs are audited annually to ensure they meet certain baseline requirements, and are graded on their ability to do so. CAs that are assessed annually will publish the audit reports on their websites.
Support
What kind of support is available to help with technical issues or installation assistance?
Every website that does business on the Internet is potentially vulnerable. If your server goes down, or there is some other kind of technical glitch with your SSL/TLS security, you will want to have access to support. And, as we’ve all experienced, there is a difference between the perception of support and getting real answers to your technical conundrums. SSLShopper is a great resource when checking up on what CAs offer exceptional service versus those that get by on providing adequate service to their customers.
Verification Practices
Are certificates issued by the CA passed through a verification procedure? Has the procedure ever been breached?
What matters to your customers is that (1) their private information is safe on your website and (2) they are dealing with an actual entity that can be trusted. What matters to you then is that your customers have no reason to believe that either of these conditions is even remotely threatened. Although the CA is not directly responsible for protecting websites, the verification and issuance of SSL/TLS certificates that they are responsible for provide the assurance and protection ability your customers are expecting when they transact on the Internet.
While Verification is sometimes experienced as an annoying roadblock, keep in mind that leading CAs employ their own verification departments and put a lot of work into devising processes that make sure no evildoers get a hold of one of their SSL/TLS certificates. Once again, SSLShopper is a great resource for getting feedback on which CAs do verification the right way.
Generally, there are three things CAs verify to qualify certificate applicants (more if the applicant is requesting an Extended Validation certificate):
- Identity
- Domain ownership/control verification
- Employment verification of individuals applying for SSL/TLS certificate on behalf of organization
Certificate Management System
Does the CA offer a way to manage inventory and easily keep track of your certificates?
The best CAs will enable their customers with the ability to manage SSL/TLS certificate inventory, expiry dates and all other kinds of data that are a part of your Internet defense arsenal. The Certificate Management System will take all the guesswork out of deploying, reissuing and renewing your SSL/TLS certificates. While it is your responsibility to make sure that your networks and websites are secure, it is the CA’s responsibility to make it as easy as possible to use their technology to do so and offer security features that go beyond the certificate itself and empower security technicians to have a firmer grasp and control over their web security.
CAs that position themselves as partners in the deployment of SSL/TLS certificates and offer support such as server installation, server certificate scanning, website scanning, certificate management and discovery and responsive CRL (Certificate Revocation List) and OSCP (Online Certificate Status Protocol) responses are organized to be dependable and offer real solutions to the challenges of managing SSL/TLS security.
Local Presence
Does the CA operate out of one country, or internationally?
There are a lot CAs that only have offices in one country. For the most part, that is not a source of concern unless the CA does not operate in your country. One advantage the leading CAs have in this area is that they operate internationally and have offices or partners all over the world, which allows them to gather experience from a larger, more diverse group of customers which in turn puts pressure on them as the CA to be more agile and have even better processes, systems and customer support.
Even though some argue that large companies treat their customers like numbers, rest assured that in a business based on ensuring personal security and identity protection, you are too real to be treated like an integer. As a result, CAs will often associate with regional partners who better understand the business landscape in their home countries and already have established relationships with local businesses and the public. The synergy between CAs and their local partners both improves web security in those nations by introducing the CA’s technologies and processes to those regions as well as provides new perspective to CAs as they gather information on how to implement SSL/TLS technology in countries where business may be done differently. Thus, CAs that operate internationally have a wider variety of experiences and use cases that allow them to better anticipate security threats and develop products and services based on what they have learned.
NEXT ON PROVE IT: Why Do Malicious Cyber Attacks Have Such Cute Names?


