Is your organization ready? Do you have a data governance program or security audit? Do you know what your IT assets are? It’s important to be prepared. Many customers we speak with are unaware of the need to monitor widely in order to prevent a breach…that especially includes their SSL/TLS certificates.
What if your organization has nothing? No monitoring, no management, no audit, no policies. It’s important to start somewhere and it’s important to start as soon as possible. The Ponemon Institute reports that in many cases an audit or data governance program could have a major financial impact for your organization. “Improvements in data governance programs will reduce the cost of data breaches. Incident response plans, appointment of a CISO, employee training and awareness programs and a business continuity management strategy continue to result in cost savings when it comes to data breaches.” (Ponemon Institute Research Report).
An information security audit covers topics from auditing the physical security of data centers to auditing the logical security of databases. It highlights key components to look for and different methods for auditing in order to prevent a breach.
The cost of a data breach is permanent. Preparing for or attempting a security audit or data governance program can be a daunting task. Organizations need to be prepared to deal with and incorporate breach response into their data protection strategies.
Many organizations are moving at a rapid pace and simply coming up with the time, resources and money to implement a security audit or a plan are overwhelming.
Many organizations overlook their SSL/TLS certificates as part of this security audit.
SSL/TLS certificates are a big part or your web security strategy and should also be audited and reviewed regularly. The CA Browser Forum is the governing body for all certificate authorities like Entrust Datacard. It stipulates the rules and guidelines to which Certification Authorities should adhere to. Entrust Datacard helps to get you the latest information by pushing notifications to customers via the Entrust Certificate Service Cloud. Along with regular touch points of the Entrust Datacard account management program, our resident SSL certificate expert and Certificate Authority Board Member, Bruce Morton, shares news regularly through the IdentityON Blog.
In September Google announced that Google’s Chrome will start to indicate HTTP sites that transmit passwords or credit cards as “non-secure” sites that transmit passwords or credit cards as “non-secure”. Google indicated they will become increasingly stringent as part of a long term plan to mark all HTTP sites as non-secure to end users.
Since the end of 2014 there has been a push for HTTPS everywhere. In June 2015, the White House issued an HTTPS-only standard directive, requiring that all publicly accessible Federal websites and webs services only provide service through a secure HTTPS connection. Does your organization have a plan to increase use of SSL/TLS certificates to keep up with these security advances? Will you proactively manage your SSL/TLS server settings? While this push for HTTPS continues, we still see a great deal of failing scores when scanning servers for certificate implementation and best practices.
Are all SSL/TLS certificates created equal? EV? OV? Oh My….
SSL certificates are grouped by type of verification or authentication of identity.

Organization Validation (OV) certificates provide a verification of the identity of the organization or individual purchasing the SSL/TLS certification. Certification Authorities (Entrust Datacard) that issue these certificates check with third parties to establish the official name and location.
If your organization has deployed Wildcard certificates or is considering deploying them, you need to consider and weigh the convenience and risk.
Sharing private keys and increasing the private key value
- When sharing private keys on multiple servers/appliances you increase the risk of also sharing vulnerabilities. A prime example is Heartbleed, if a company hosted one public facing web site on a server that was vulnerable to the Heartbleed bug with other platforms (e.g. MS IIS, Exchange, Cisco) then an attacker that breached the affected Heartbleed server could listen in on the traffic from all other servers that the same private key was shared with.
- Private key value, when you deploy a certificate to a web server the private key has the responsibility of securing all the traffic for that web server. The question is, how much is that traffic worth to a company if it was breached? Now add on any other server traffic that the same private key is being used on, this gives you a dollar figure that you can determine how much a breach will impact your company. The higher the private key value, the more risk to the company.
Which type of SSL/TLS certificate do I need? Compare different types of certificates.
Has your organization applied the correct certificates and have those certificates been selected to optimize consumer trust?
Certificate Transparency
Certificate Transparency (CT) provides an open framework for monitoring and auditing SSL/TLS certificates in nearly real time. Certificate Transparency makes it possible to detect SSL/TLS certificates that may have been mistakenly issued by a Certificate Authority or maliciously attained. Illegitimate certificates have been issued in the past and used to masquerade as legitimate, secure websites that appear to be authentic fooling end users.
Have you migrated from SHA-1?
SHA-1 (Secure Hash Algorithm) has been in use since the late 1990’s. SHA-1 certificates are found to have vulnerabilities and are no longer considered secure for ongoing use. Major browsers have announced that they will no longer accept SHA-1 SSL/TLS certificates by January 1, 2017. Do you have SHA-1 certificates still in use? SHA-2 is the new industry standard and organizations require a plan for replacement. By using a tool like Entrust Discovery Agent and use our Discovery Manager to find what SHA-1 certificates you may have still lurking.
This migration will require coordination of people, process and technology across the organization. Check out the Entrust migration guide.
SSL/TLS use is increasing. Putting a certificate on it and forgetting it isn’t the answer
Applying the certificate is the first step. Configuration and adherence to web security guidelines are a key part of web security. Two scanning sites that can help check your configuration are the SSL Server Test by Qualys and “Observatory” by Mozilla. The SSL Server Test has been incorporated into the Entrust Certificate Services so that every time our customers log in, they can view their certificate ratings.
SSL Server Test by Qualys – https://entrust.ssllabs.com/
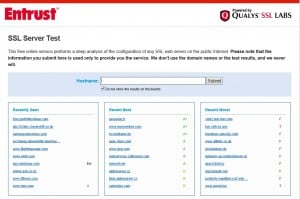

The SSL Server Test by Qualys is built in functionality to the Entrust Certificate Service so that all certificates and websites can be monitored for their ratings.
Observatory by Mozilla – https://observatory.mozilla.org/
Many organizations we speak with are unaware of how many Certificate Authorities they have used over the years and not truly sure of the number of certificates deployed and their locations. Entrust can also assist with this. The Entrust Discovery Agent can help you understand how many Certificate Authorities you really have, as well as what certificates you have deployed and where – even your non-Entrust certificates.
Get Started
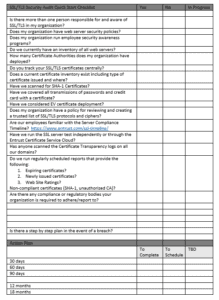
Have nothing to start with? Below is a quick checklist to get you started – have I forgotten anything? Any checklists that you’d like to share?
Entrust Datacard can help your organization get started in your SSL/TLS security audit by helping you create your SSL/TLS Asset list, creating an SSL/TLS threats list and identifying areas for intrusion prevention.
Mozilla Rapid Risk Assessment –
https://wiki.mozilla.org/Security/Risk_management/Rapid_Risk_Assessment#Rapid_Risk_Assessment
Mozilla Risk Table –